TE-SYSTEM's approach to secure anynode
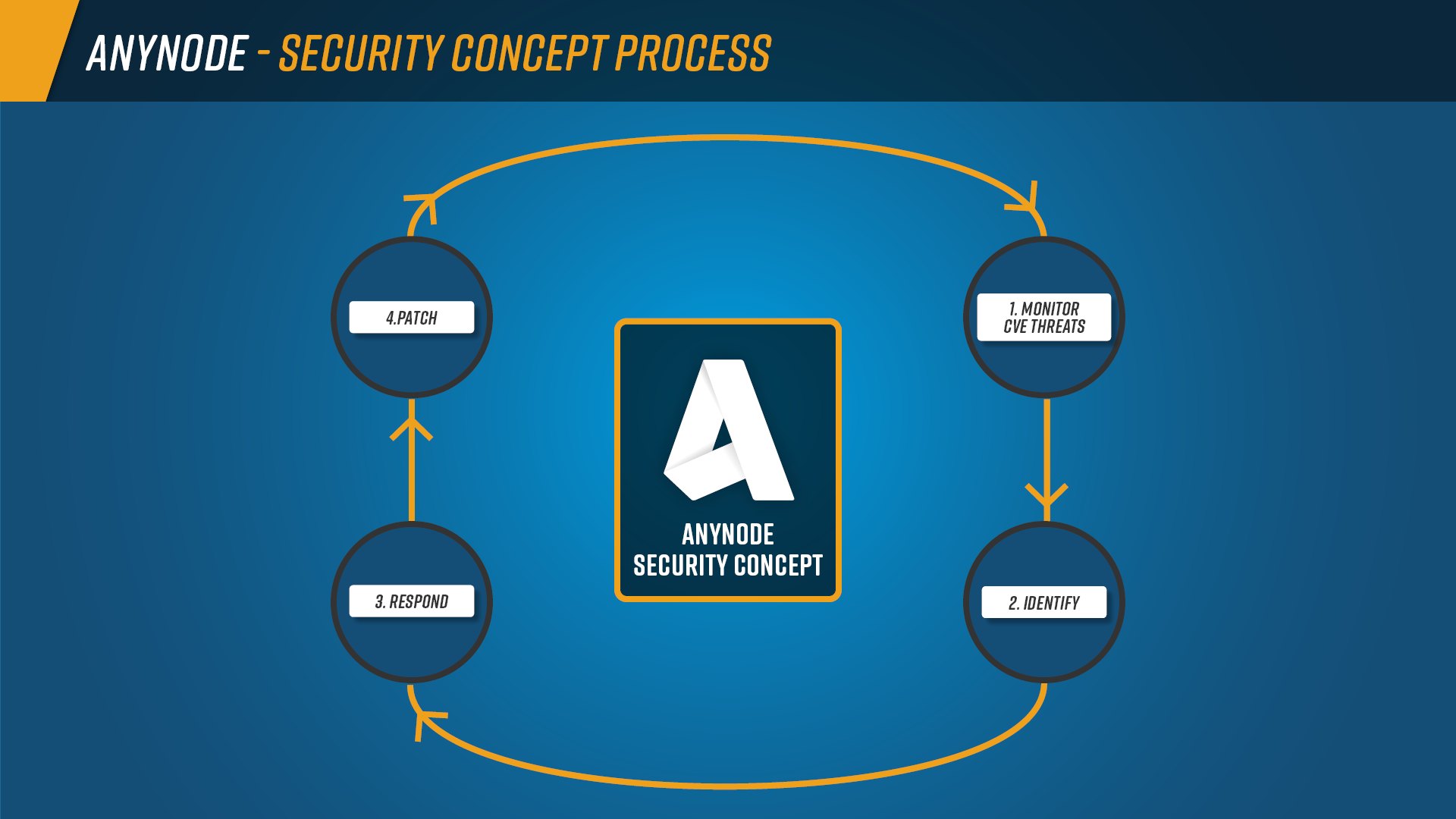
TE-SYSTEMS ensures that anynode remains secure and resilient by conducting regular security assessments and implementing proactive vulnerability tracking.
Key security measures
-
Continuous Open-Source CVE Threat Analysis: TE-SYSTEMS actively monitors and evaluates newly reported vulnerabilities in open-source components, determining the necessary response on a case-by-case basis.
-
Structured Vulnerability Handling: Threats identified from internal tests, external audits, and customer reports are analyzed based on severity and impact. High-risk vulnerabilities trigger an immediate Product Notice with mitigation steps and a fix date.
-
Security Patch Releases: Fixes are rolled out according to a structured update process to ensure ongoing protection.
Through these proactive security practices, anynode stays protected against emerging threats while maintaining system integrity and reliability.
What You Will Gain from This Document
By the end of this document, you will have a clear and structured understanding of:
-
The security measures embedded in anynode SBC: including continuous security audits, proactive vulnerability tracking, and structured threat mitigation.
-
How anynode pro actively prevents, detects, and mitigates security threats: leveraging Open-Source CVE Threat Reports Analysis, structured vulnerability handling, and rapid security patching.
-
The process TE-SYSTEMS responds to a threat: after detecting a threat, we respond internally by opening a work item and promptly notifying our development team to resolve the issue.
-
The compliance standards and industry best practices that guide our security approach: ensuring alignment with regulatory requirements and enterprise security expectations.
With this knowledge, you can be confident that anynode SBC is built to meet the highest security requirements, providing a safe and reliable communication infrastructure for your organization.