Accessing anynode WMI
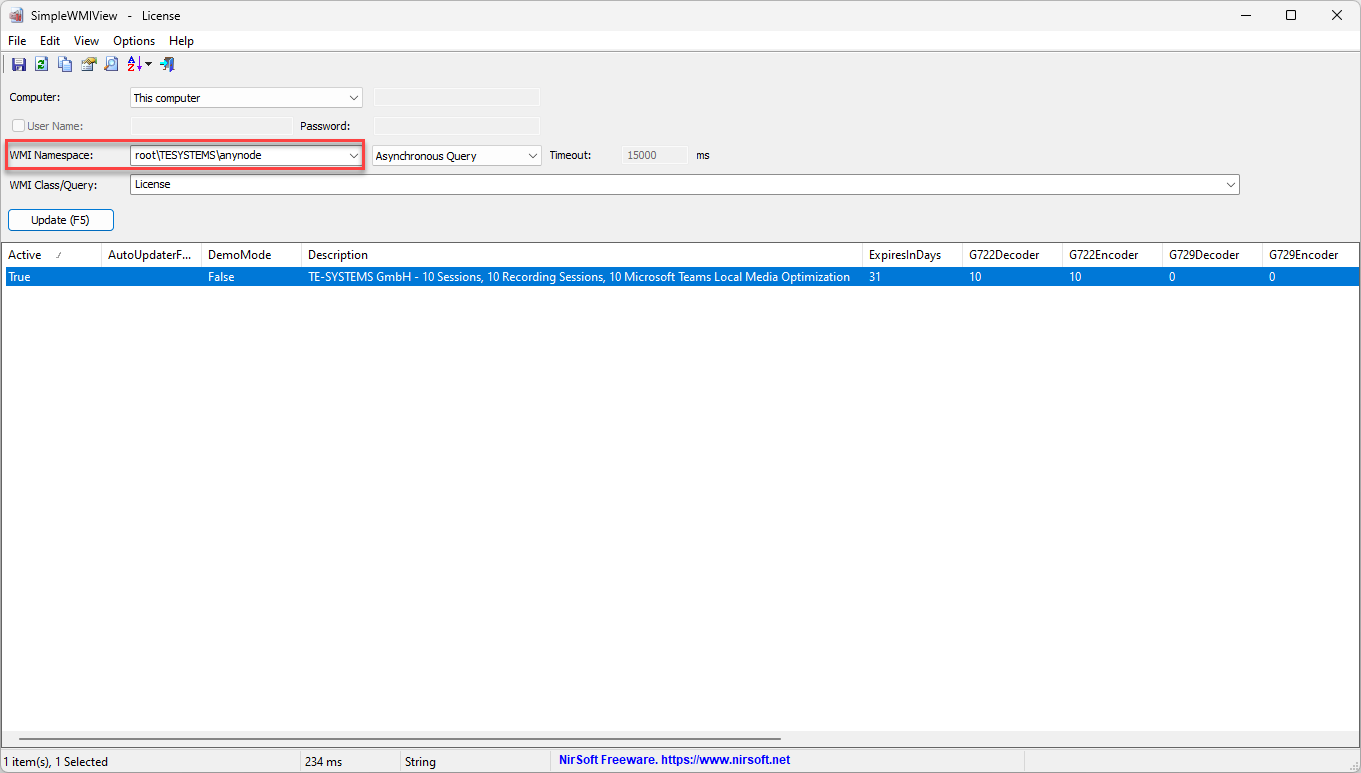
Retrieve anynode data via WMI and visualize it using Simple WMI Viewer for Windows for further monitoring and analysis.
SimpleWMIView is a lightweight Windows tool that presents WMI query results in a clear, tabular format. It allows you to effortlessly export data to text, CSV, tab-delimited, HTML, or XML files, or copy selected items to the clipboard for easy pasting into Excel or other spreadsheet applications. Simple WMIView is an excellent tool for both beginners and experienced users who want a fast, straightforward way to interact with WMI without the complexity of scripting or using command-line tools. It's particularly valuable for applications like anynode, where monitoring or configuration data can be accessed via WMI for analysis or integration.
Download and install SimpleWMIView from a trusted source. Open the application once installed.
Set up the connection:
Namespace: Enter the WMI namespace used by anynode:
root\TESYSTEMS\anynode
If you use the drop-down menu, choose TESYSTEMS and add anynode
Credentials: If accessing a remote machine, specify the username and password. Use the local administrator account for local machine access.
Select the desired WMI class and run a query.
Click on .
Access via WinRM and EnablePSRemoting
WMI remote access via Windows Remote Management (WinRM) offers several advantages:
Enhanced Security: Communication is encrypted using HTTPS or Kerberos, supporting modern authentication methods.
PowerShell Integration: Seamlessly works with PowerShell cmdlets for advanced scripting and automation.
Firewall-Friendly: Uses fixed ports (TCP 5985/5986), simplifying firewall configurations.
Scalable Management: Supports centralized automation and integration with tools like Ansible and Terraform.
Cross-Platform Capability: Enables management of both Windows and non-Windows systems.
Modern and Reliable: Provides a robust framework for secure, scriptable remote management.
To make a WMI query to anynode via Windows Remote Management (WinRM), you need to ensure that several configurations and prerequisites are in place.
Enable Windows Remote Management (WinRM) on the Target System
On the remote system (the one running anynode), you need to enable WinRM if it isn't already enabled. This can be done through the following PowerShell command:
Enable-PSRemoting -Force
This enables the system to accept remote PowerShell commands via WinRM.
Configure the Windows Firewall
Make sure that the firewall on the remote system allows WinRM traffic. Typically, the necessary firewall rule can be enabled
with the following command: New-NetFirewallRule -Name WINRM -DisplayName "Windows Remote Management" -Enabled True
-Protocol TCP -LocalPort 5985
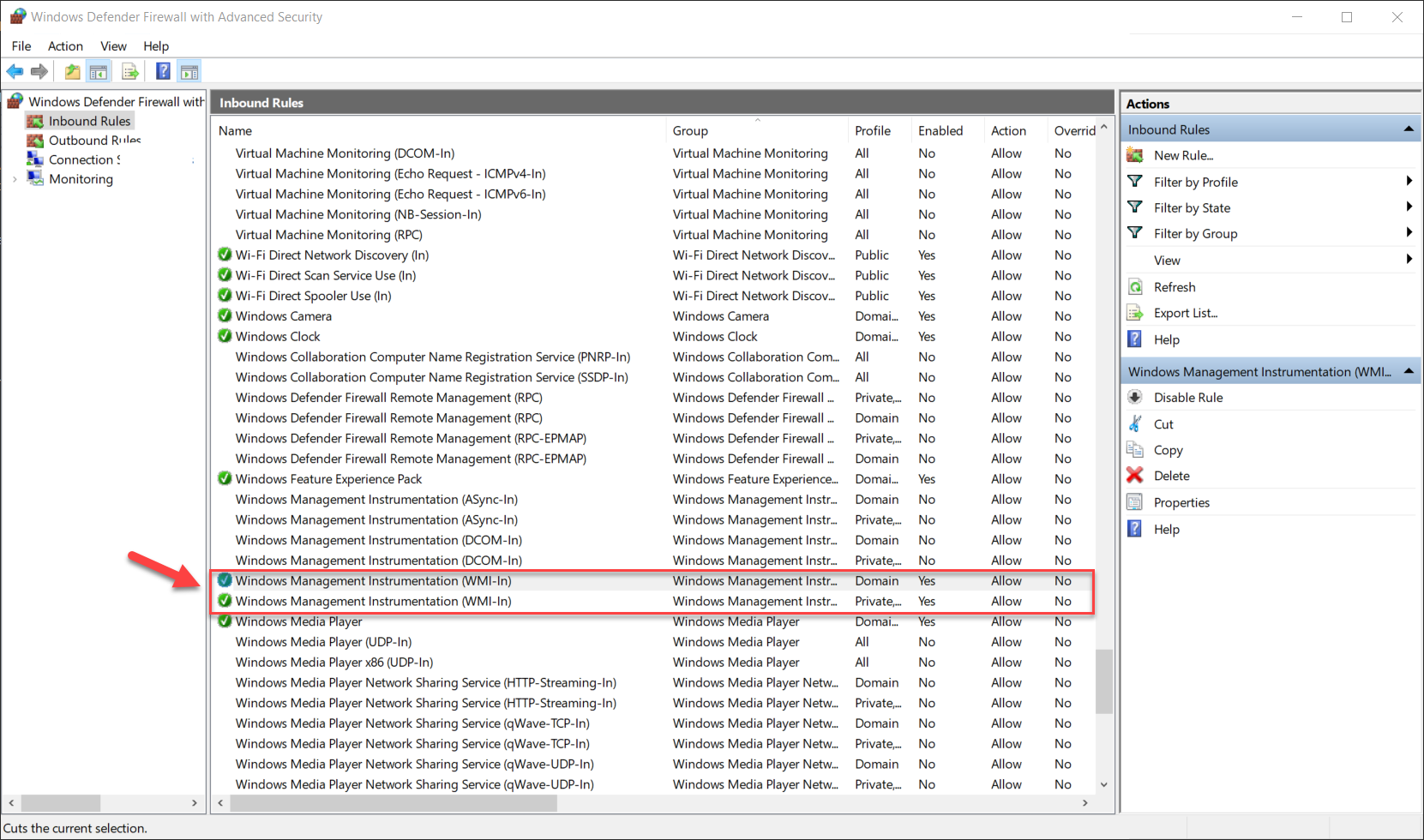
Allowing the WMI-In rule in the Windows Defender Firewall with Advanced Security is crucial when using a remote WMI query to anynode. The WMI-In rule permits inbound traffic on the ports and protocols required for WMI communication. Without this rule, the firewall blocks WMI requests from remote systems.
In the left pane, select Inbound Rules.
Find rules named Windows Management Instrumentation (WMI-In).
Right-click the rule and choose Enable Rule.
Limit access to specific IP addresses under the Scope tab for tighter security.
Opening port 135 to the public is strongly discouraged due to its inherent security risks and the nature of the port.
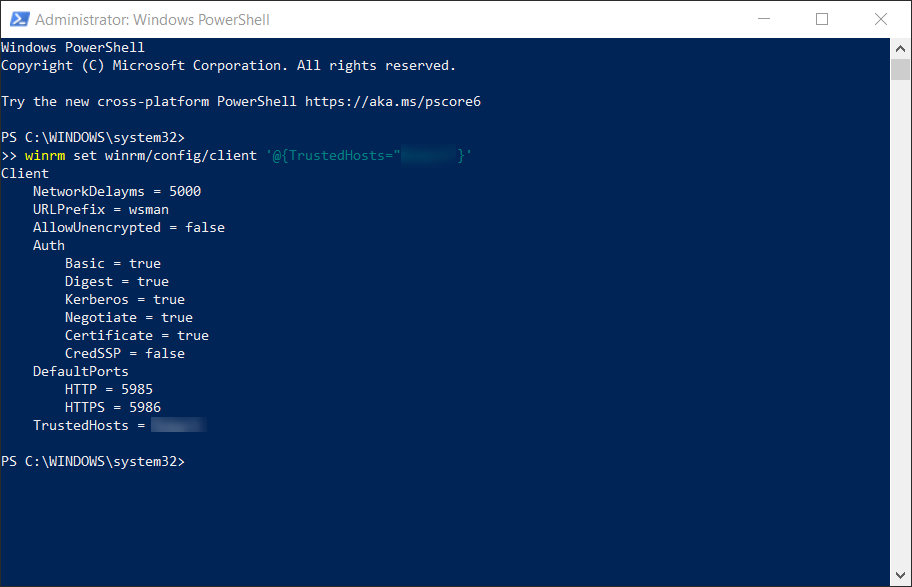
Allow a trusted host in the Windows Remote Management (WinRM) configuration with the command:
winrm set winrm/config/client '@{TrustedHosts="*"}'
This enables your system to connect to remote computers for management tasks over an unsecured or non-domain-joined environment. This is especially important when using protocols like WMI (Windows Management Instrumentation) remotely.
Instead of '*', specify trusted hosts explicitly.
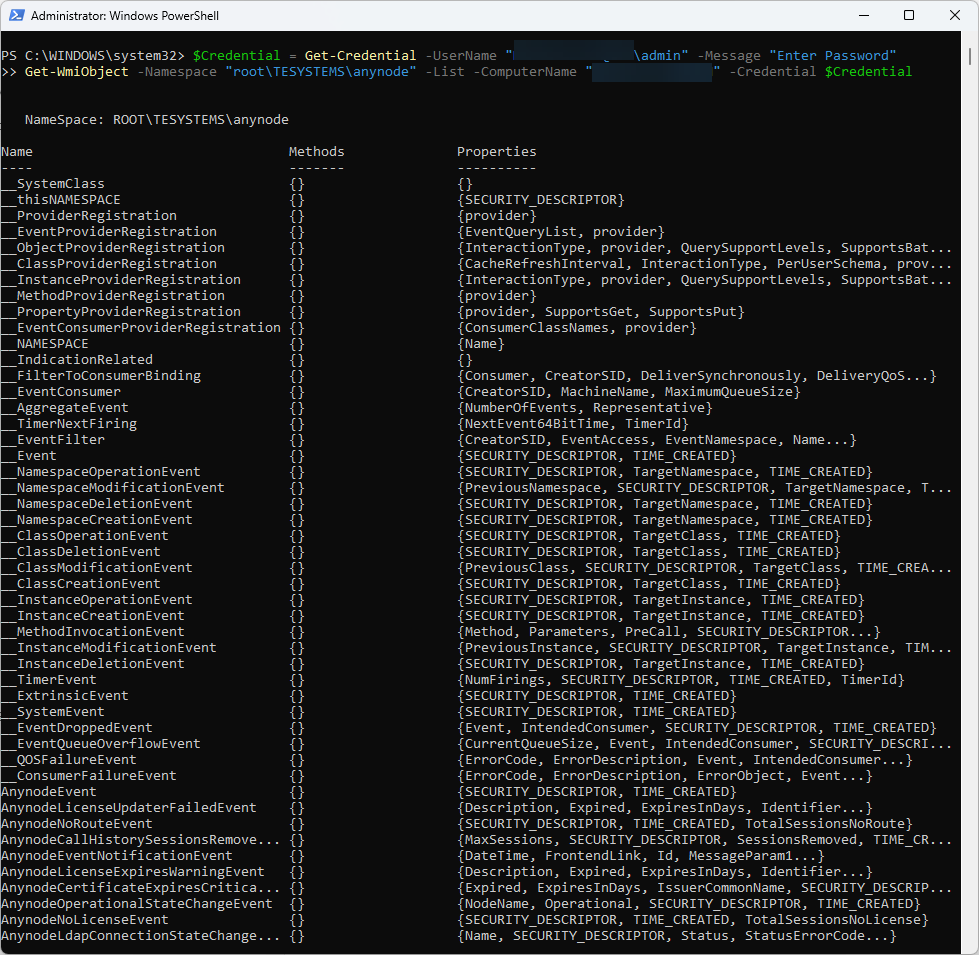
Establish Remote WMI Connection
To query WMI data from a remote system, you can use PowerShell or another WMI query tool. Here's how to use PowerShell.
Use the correct Namespace root\TESYSTEMS\anynode
Get-WmiObject -Namespace "root\TESYSTEMS\anynode" -List -ComputerName "RemoteComputerName" -Credential $Credential
>> $Credential = Get-Credential -UserName "RemoteComputerName\admin" -Message "Enter Password"
Replace <RemoteComputerName> with the name of the remote system.
Check if the WMI class returns values
Use the following command to display all properties and their values from the System class:
Get-WmiObject -ComputerName "computer name" -Namespace "root\TESYSTEMS\anynode" -Class "System" -Credential (Get-Credential)
All properties, including AnynodeVersion, should be displayed with their respective values.
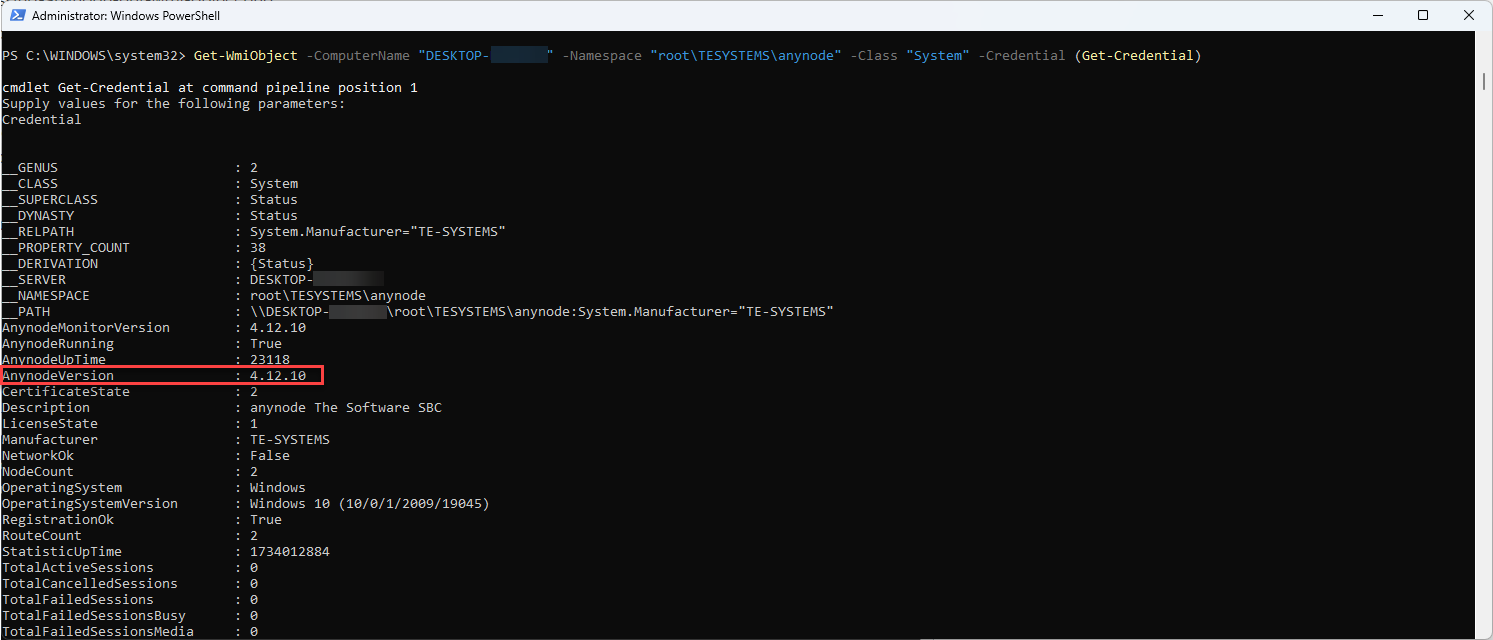
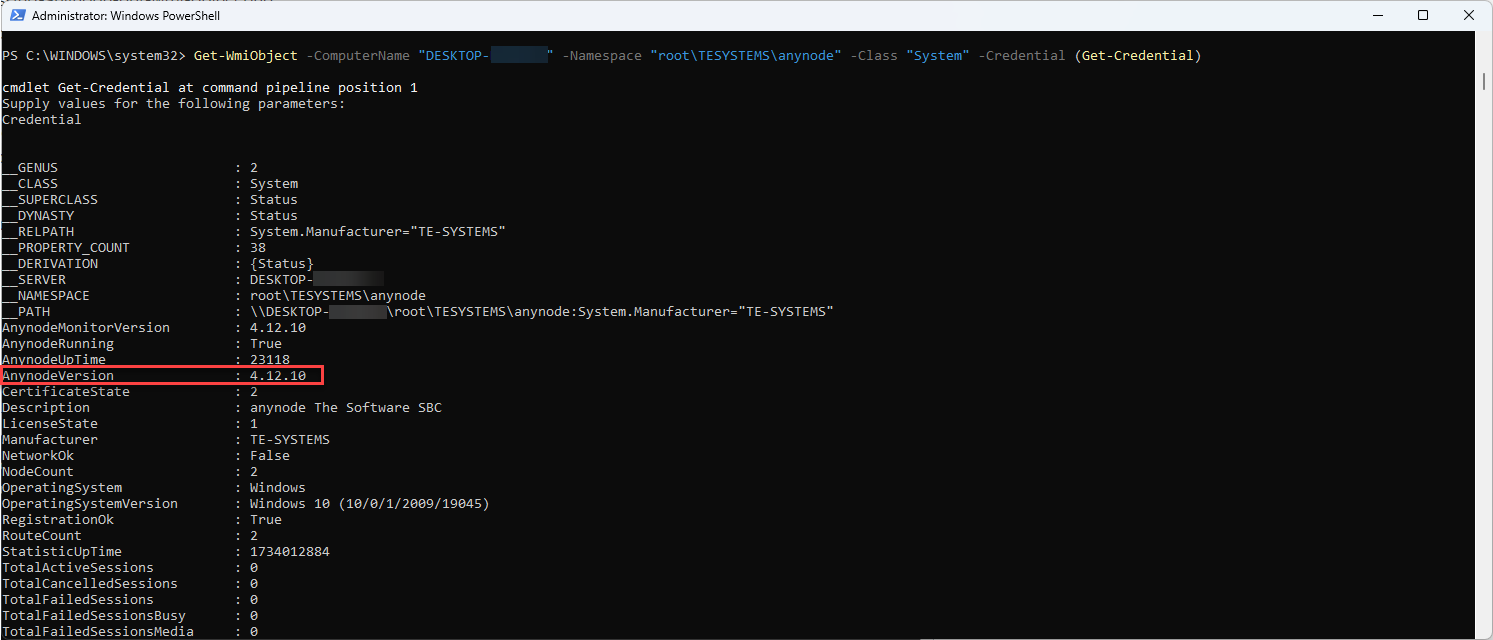
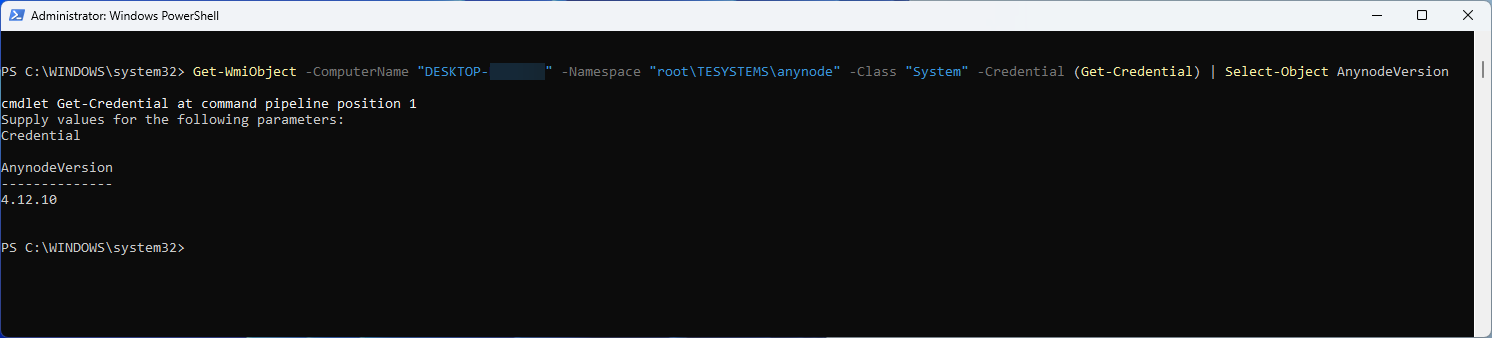
This PowerShell command retrieves information about the System WMI class
from the root\TESYSTEMS\anynode namespace on a remote computer (DESKTOP- computer name) and filters
the output to show only the AnynodeVersion property.
Get-WmiObject -ComputerName "computer name" -Namespace "root\TESYSTEMS\anynode" -Class "System" -Credential (Get-Credential)
| Select-Object AnynodeVersion
Remote Access via DCOM-In and SimpleWMIView
Use DCOM and SimpleWMIView only in legacy or quick-access scenarios. For ongoing or secure management, prefer WMI access via WinRM. DCOM relies on less secure mechanisms, making it vulnerable to attacks without proper network protections.
Opening port 135 to the public is strongly discouraged due to its inherent security risks and the nature of the port.
Allowing Windows Management Instrumentation (WMI) (DCOM-In) in the Windows Defender Firewall with Advanced Security is necessary for remote WMI queries to function because WMI relies on DCOM (Distributed Component Object Model) for communication between systems.
DCOM-In Rule: Enabling the DCOM-In rule allows the WMI service to accept remote requests and manage the dynamic ports required for communication.
On the system where anynode is running, enable the DCOM-In rule in Windows Defender Firewall with Advanced Security.
Press Win + S, type "Windows Defender Firewall with Advanced Security", and open
it.
Locate the DCOM-In Rule
In the left-hand panel, click Inbound Rules.
In the list of rules, search for Windows Management Instrumentation (DCOM-In).
You may need to scroll or use the filter in the Actions pane.
Right-click on the Windows Management Instrumentation (DCOM-In) rule.
Select Enable Rule.
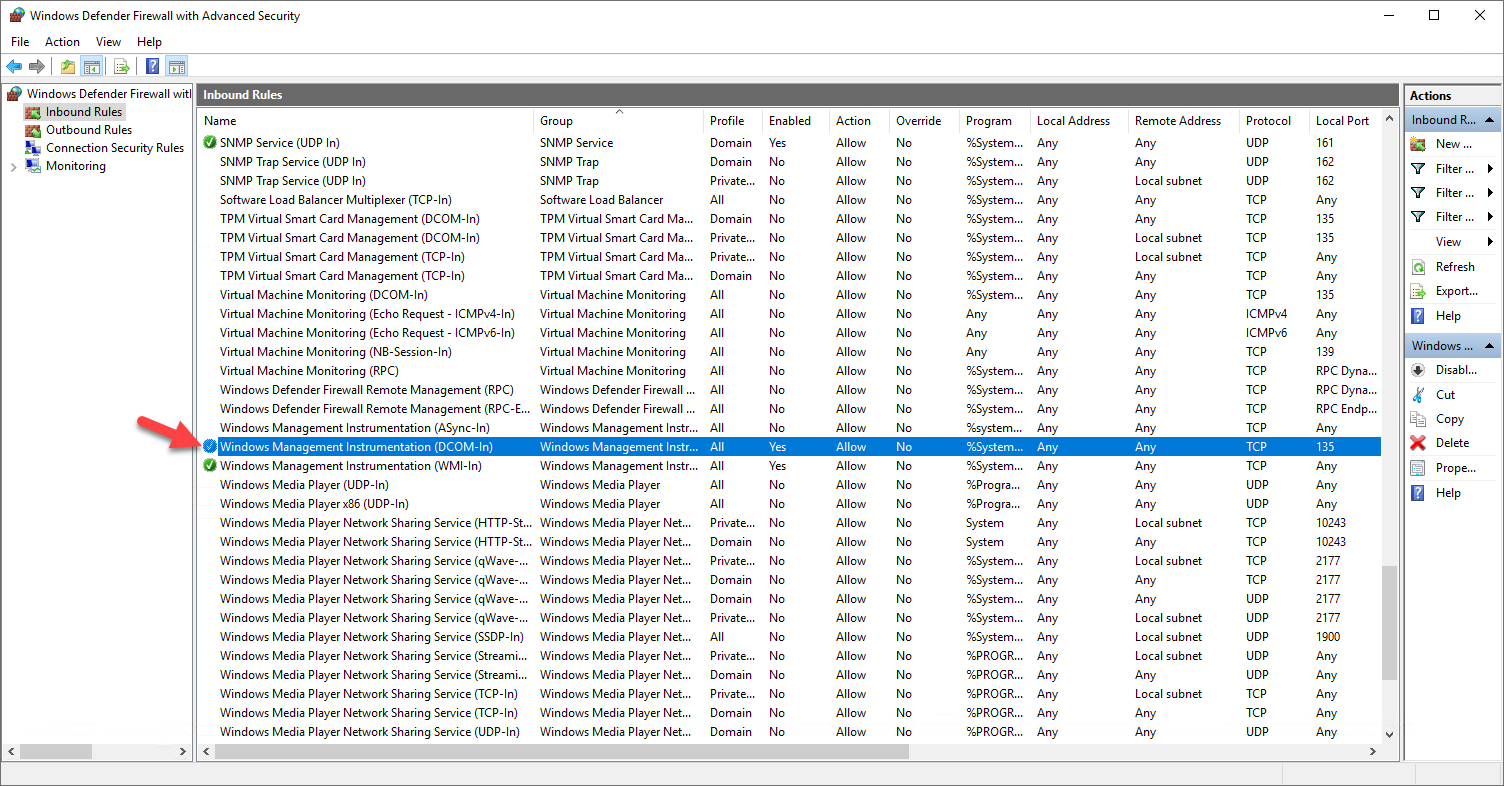
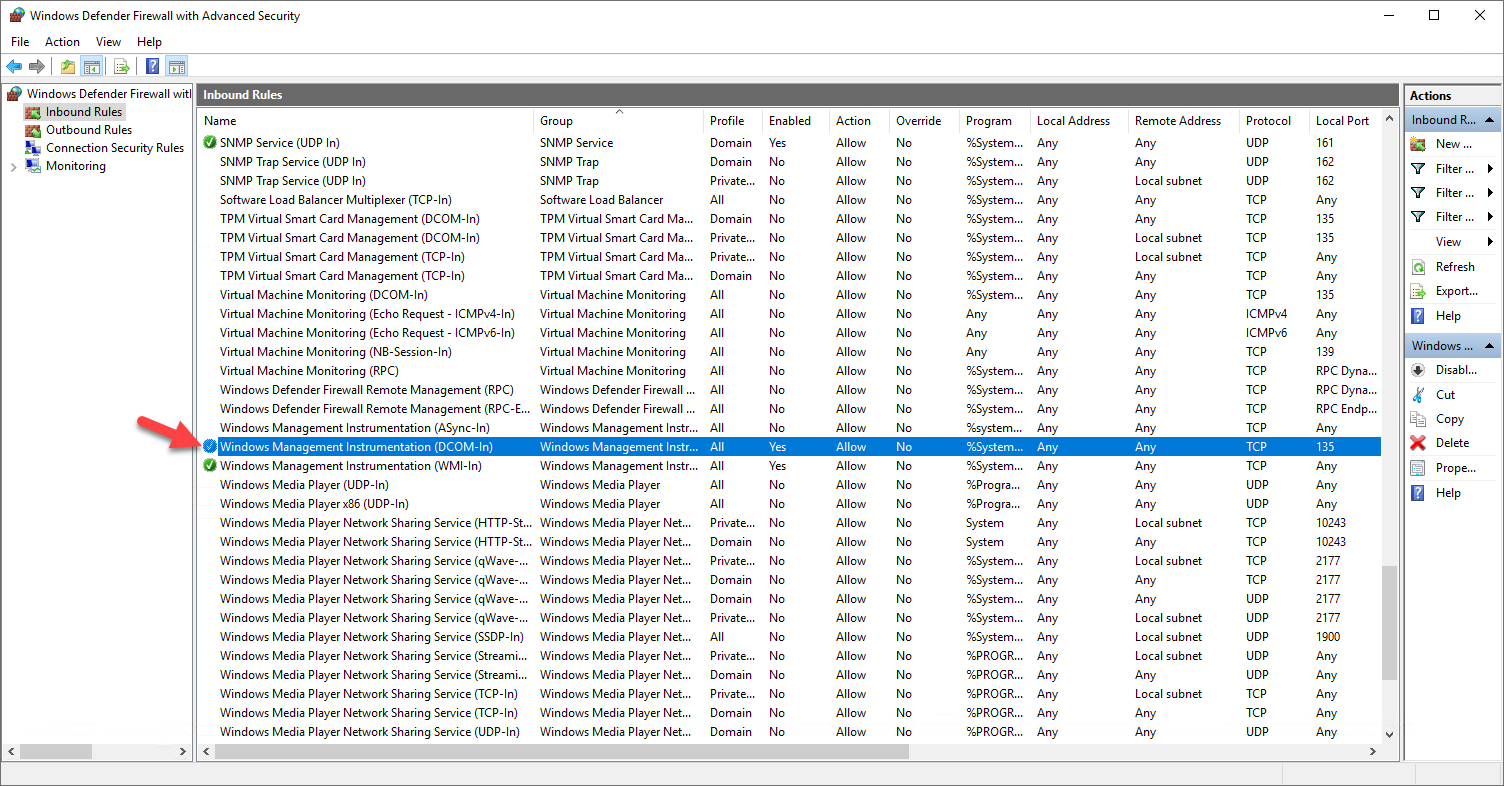
Right-click the rule again and select Properties.
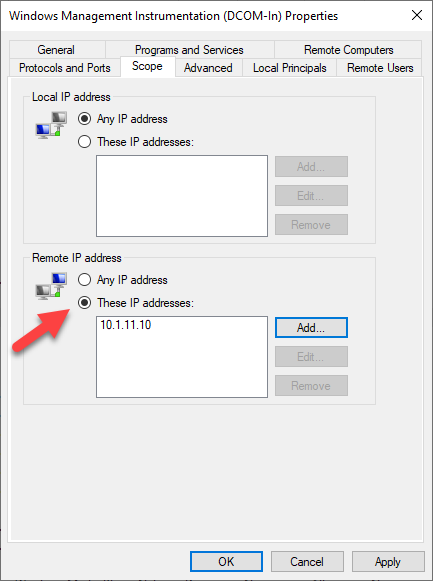
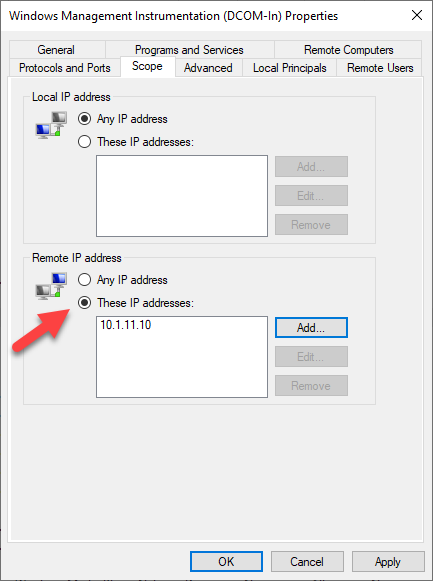
Go to the Scope tab:
Specify Remote IP addresses (trusted IPs) to limit where the rule applies.
Confirm the changes. Click .
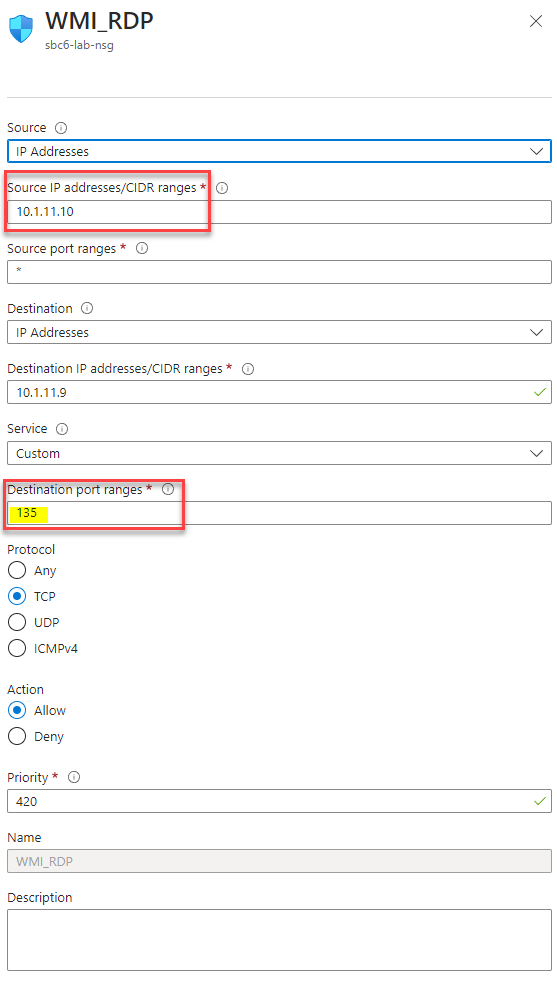
If the anynode system is running on Azure, you need to allow TCP port 135 in the firewall rules because Windows Management Instrumentation (WMI) relies on Distributed Component Object Model (DCOM) for remote communication. TCP port 135 is used by the DCOM Service Control Manager to establish the initial connection between the client and the server.
It is highly recommended to limit access to TCP port 135 to a specific source address or range of addresses when configuring firewall rules for remote WMI queries.
To restrict access to TCP port 135 to a specific source address in Azure, you need to configure an Inbound Security Rule in the Network Security Group (NSG) associated with your virtual machine's subnet or NIC.
For detailed guidance, refer to the Microsoft Azure NSG documentation.
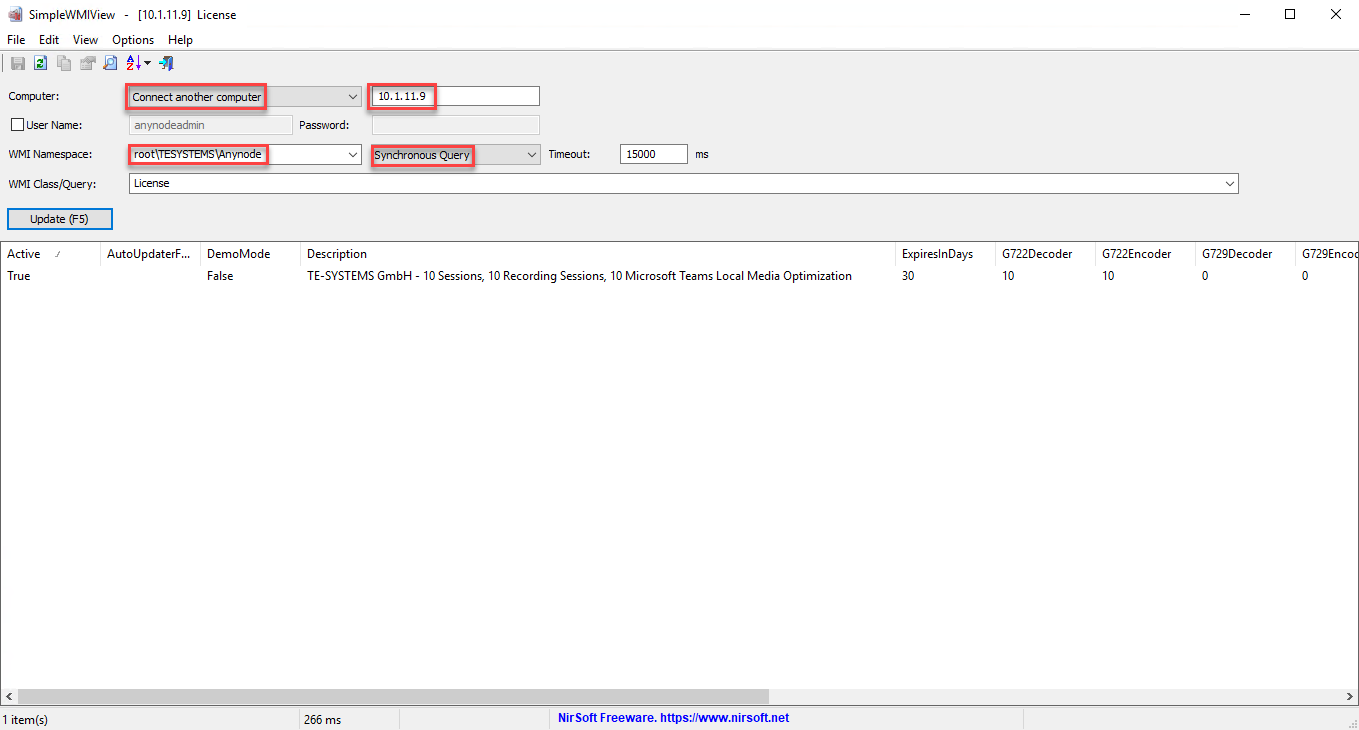
Our example
We will use SimpleWMIView to make a WMI query from the IP address configured as the Remote IP address on the anynode system.
Open SimleWMIView.
Choose Connect another computer
Enter the IP address of the anynode system.
Use the correct WMI Namespace: root\TESYSTEMS\Anynode
Switch to Synchronous Query
Choose a WMI Class.
Click on .
PowerShell
PowerShell is the most efficient tool for working with WMI. It allows you to query anynode-specific WMI namespaces, classes, and properties.
Steps to Query WMI Information with PowerShell
Open PowerShell:
Press Win + S, search for PowerShell, and run it as an administrator.
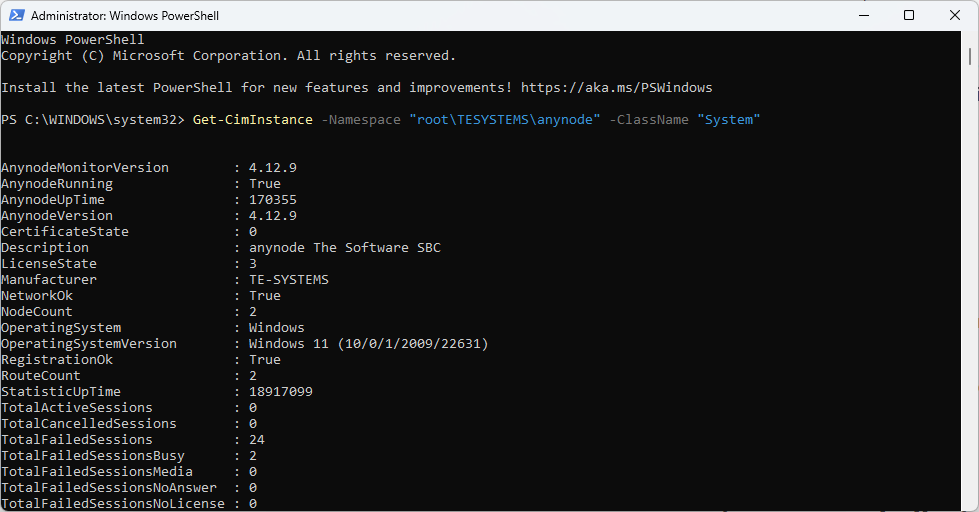
Query the anynode Namespace:
Use the Get-CimInstance cmdlet to retrieve information from the anynode namespace.
Get-CimInstance -Namespace "root\TESYSTEMS\anynode" -ClassName "System"
Retrieve Specific Properties: You can filter specific properties or objects within the anynode namespace:
Get-CimInstance -Namespace "root\TESYSTEMS\anynode" -ClassName "Status"
Subscribe to Events: You can monitor events related to anynode using PowerShell:
Register-CimIndicationEvent -Namespace "root\TESYSTEMS\anynode" -ClassName "EventClassName"
Reset Statistics: Invoke WMI methods for tasks like resetting anynode statistics:
Invoke-CimMethod -Namespace "root\TESYSTEMS\anynode" -ClassName "System" -MethodName "ResetStatistics"