Install SNMP on Windows
SNMP is considered an optional feature in Windows, and it is not installed by default. Windows SNMP service currently supports only SNMP v1 and SNMP v2c. These protocols are not encrypted. An attacker can intercept all your SNMP data and view it in plain text. Windows 10 and 11 and anynode do not support SNMP v3, an encrypted and more secure protocol. We recommend using the SNMP interface only on internal network interfaces.
Install the SNMP Service on a Windows Server 2019/2022/2025 System.
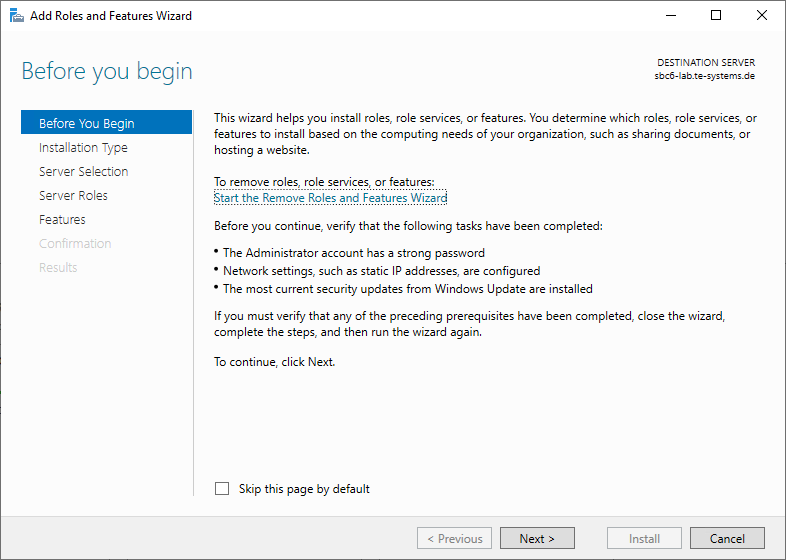
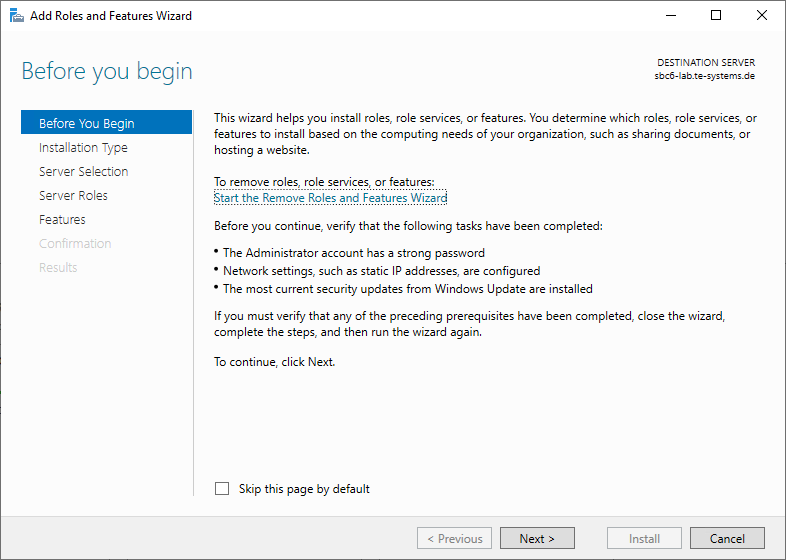
You can install the SNMP (Simple Network Management Protocol) service on Windows Server 2019 using the Server Manager GUI.
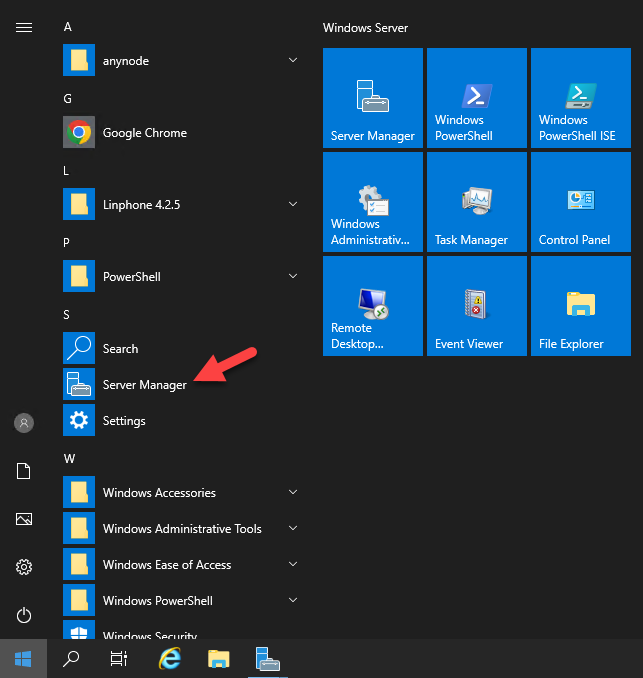
Click on the and open the Server Manager.
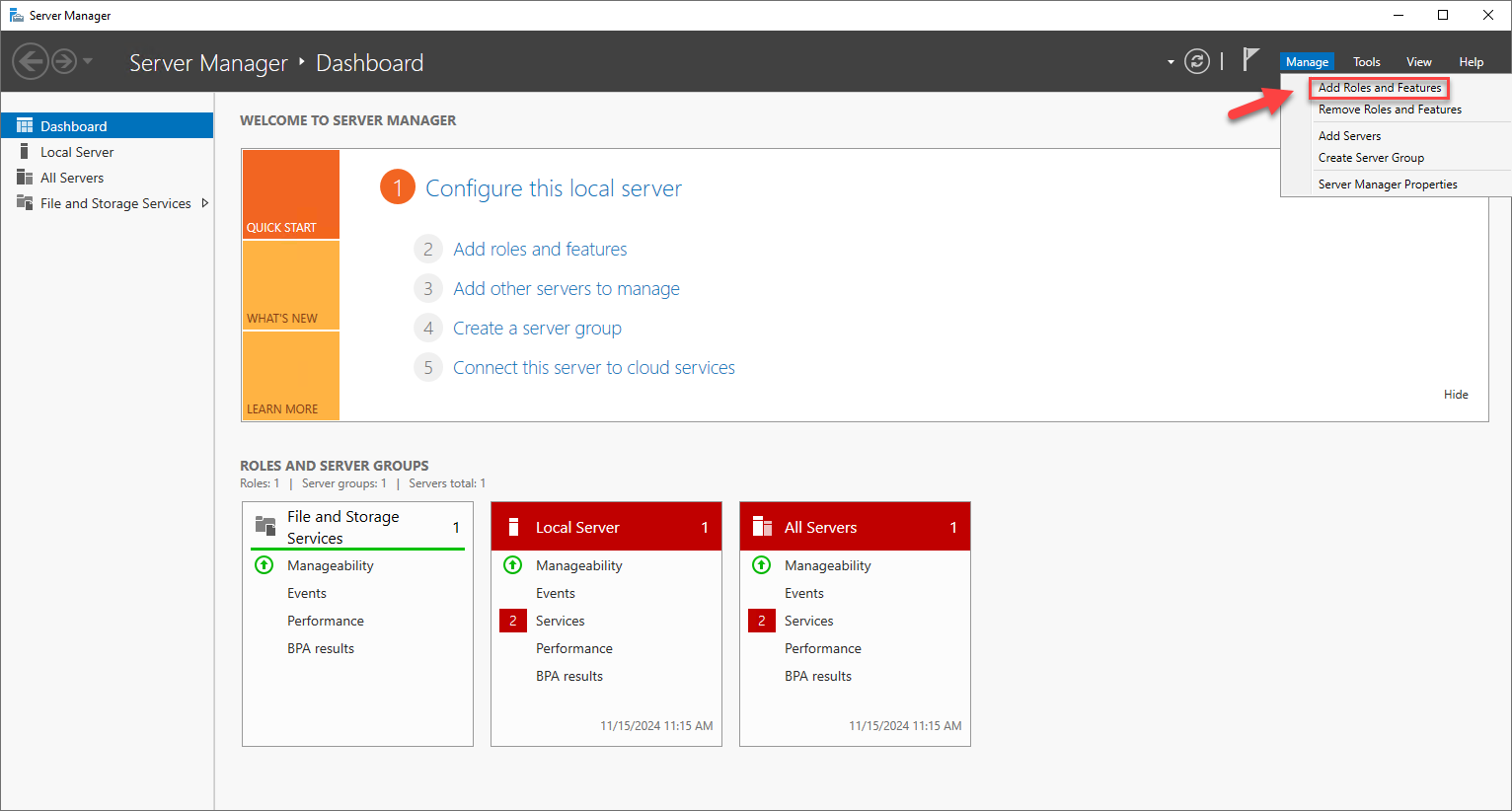
On the top right, click on Manage and select .
The Add Roles and Features Wizard will open. Verify that the following tasks have been completed:
-
The Administrator account has a strong password.
-
Network settings, such as static IP addresses, are configured.
-
The most current security updates from Windows Update are installed.
Click on the button to proceed.
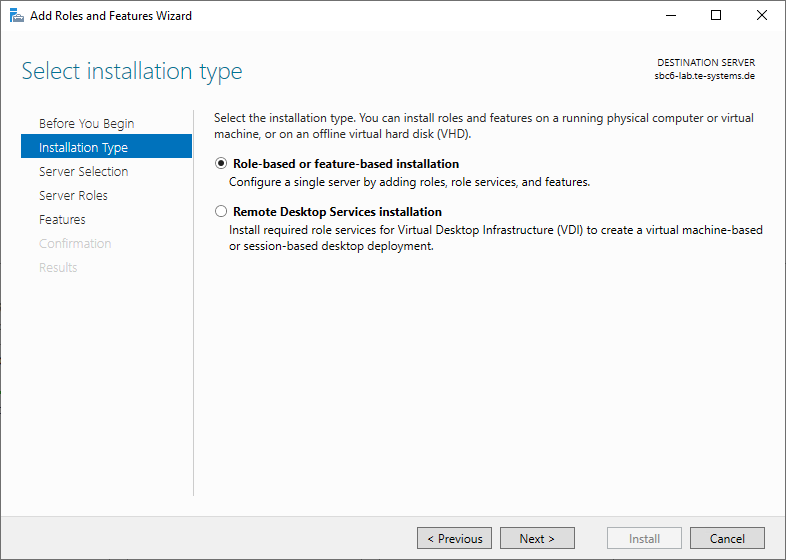
Select Role-based or feature-based installation and click .
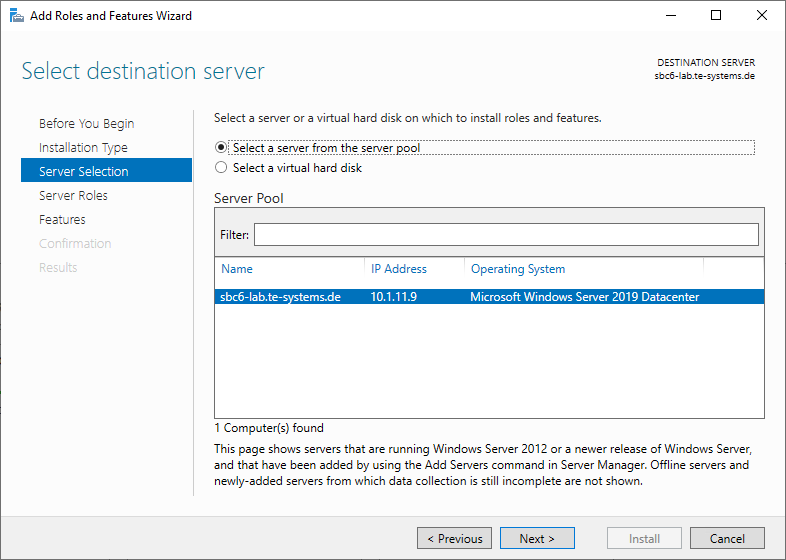
Choose the server where you want to install the SNMP service.
Click on .
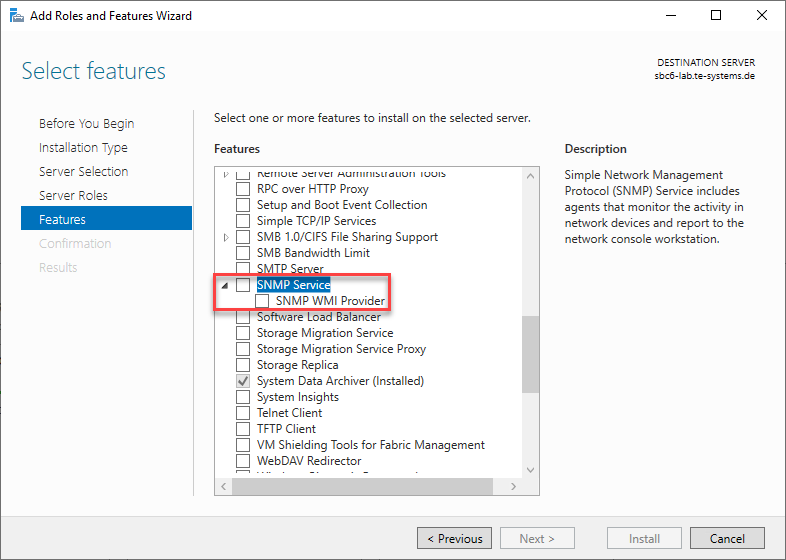
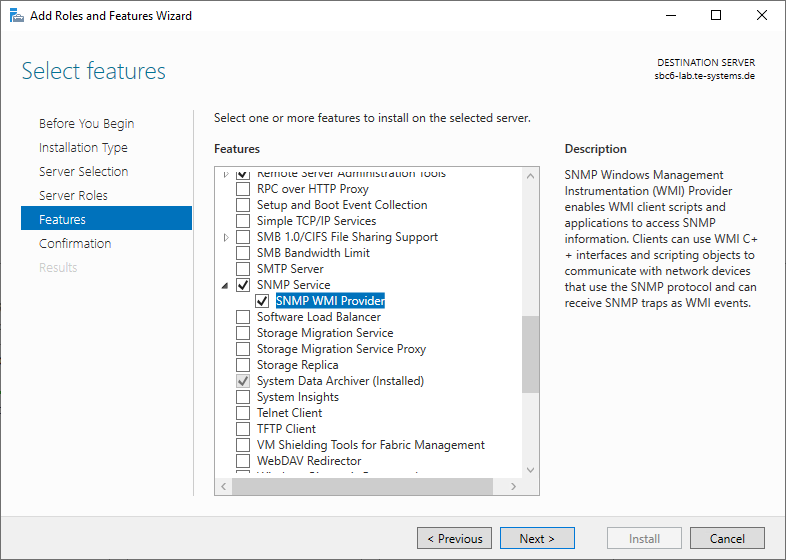
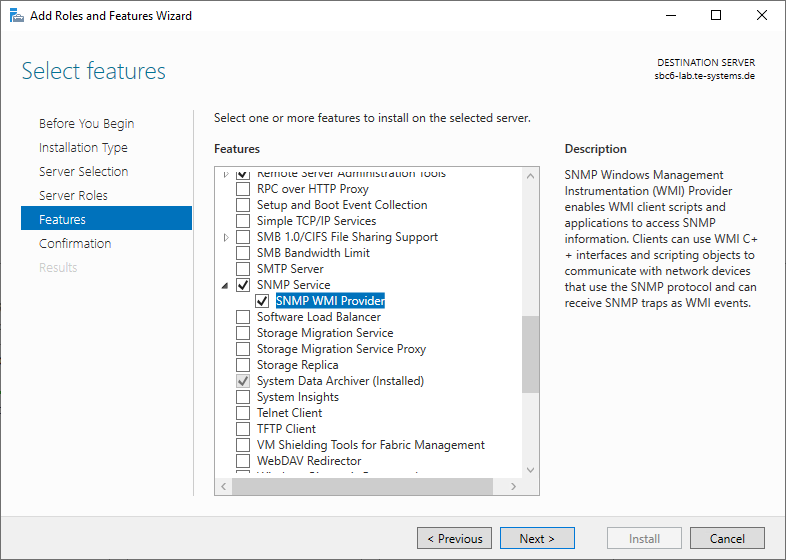
Navigate to the Features section, scroll down and enable SNMP Service.
Click and then .
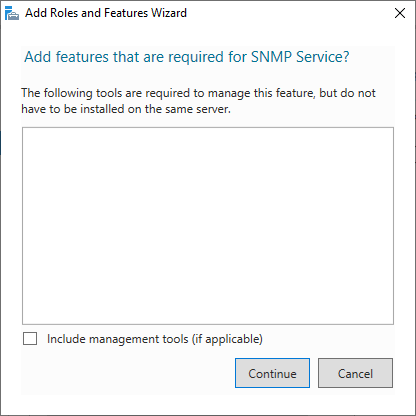
Optionally, also include management tools.
In our example, we do not use management tools.
Click .
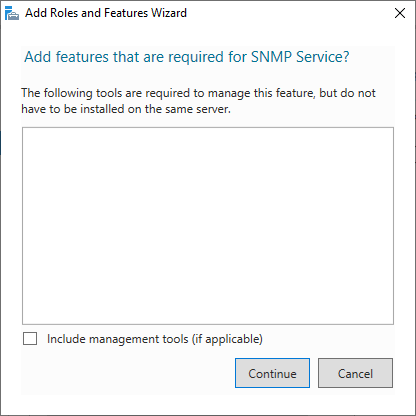
The SNMP Service including SNMP WMI provider is now selected. If not, activate SNMP WMI Provider.
Click on .
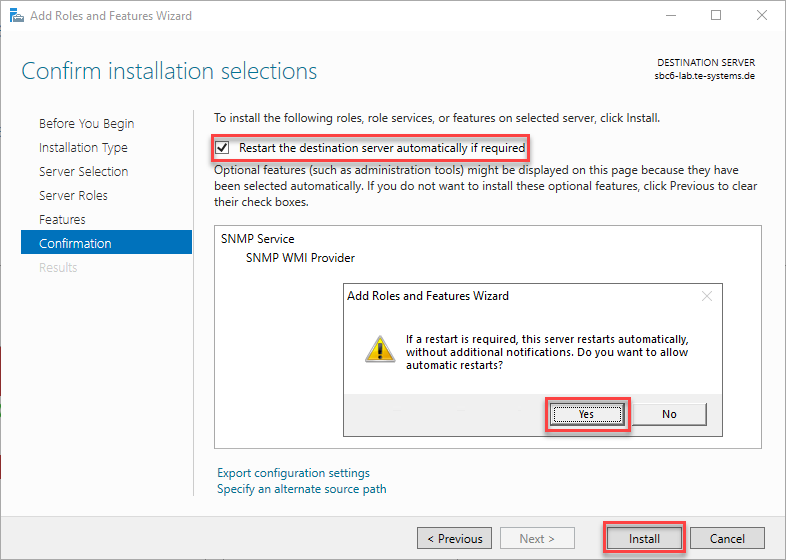
Activate Restart the destination server automatically if required.
Allow automatic restarts with .
Click on .
Wait for the installation to complete and restart the server if necessary.
Install the SNMP Service on a Windows Server 2019/2022/2025 System via PowerShell
Open the Start menu, type "PowerShell" right-click on it, and choose Run as Administrator.
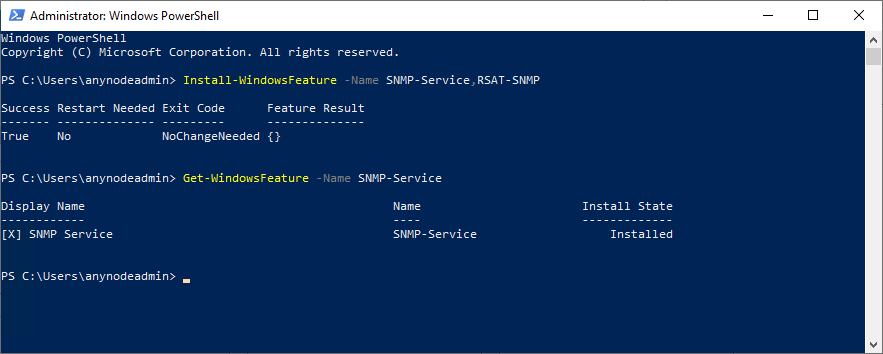
Run the following command to install the SNMP Service:
Install-WindowsFeature -Name SNMP-Service,RSAT-SNMP
To confirm the SNMP service is installed, run: Get-WindowsFeature -Name SNMP-Service
Install SNMP on Windows 10/11
Install the SNMP Service on a Windows 10/11 operating system.
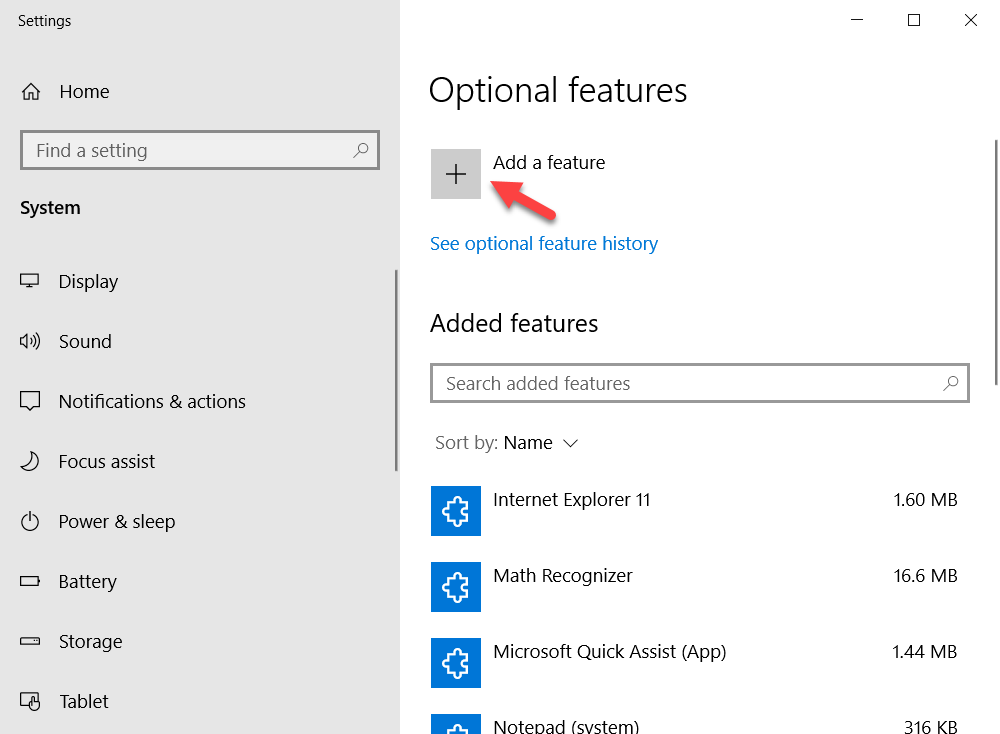
You can install SNMP via the Settings panel. Go to Apps -> Optional features -> Add an optional feature -> View features.
Select Simple Network Management Protocol (SNMP) and WMI SNMP Provider in the list of available components.
To start the installation, click .
(You will need an Internet connection to Microsoft servers).
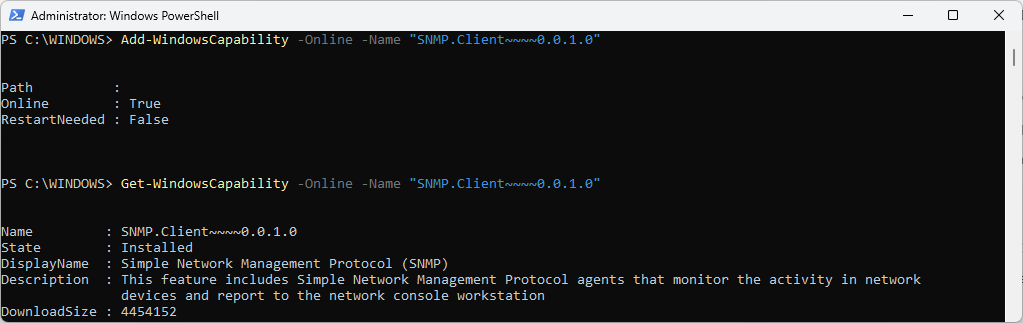
Installation via Windows PowerShell
Start Windows PowerShell as an administrator.
Run the following Add-Windows cmdlet to add the SNMP and WMI SNMP Provider features:
Add-WindowsCapability -Online -Name "SNMP.Client~~~~0.0.1.0"
Some monitoring tools (like Zabbix) may rely on WMI to query certain metrics from a Windows system. Run the following cmdlet:
Add-WindowsCapability -Online -Name "WMI-SNMP-Provider.Client~~~~0.0.1.0"
To verify the added state, run the following Get-Windows cmdlet:
Get-WindowsCapability -Online -Name "SNMP.Client~~~~0.0.1.0"
Configuration Windows
To enable external monitoring of SNMP on Windows with anynode, you need to configure specific settings in the Windows Registry (regedit) after installing the SNMP service.
Configuring SNMP via the Services app is more intuitive, safer, and better suited for most administrators. The registry should only be used for advanced or automated configurations. The Services app validates the input for fields such as community strings and permitted hosts. It prevents invalid entries that could break SNMP functionality. The registry does not provide any validation, leaving room for potential errors.
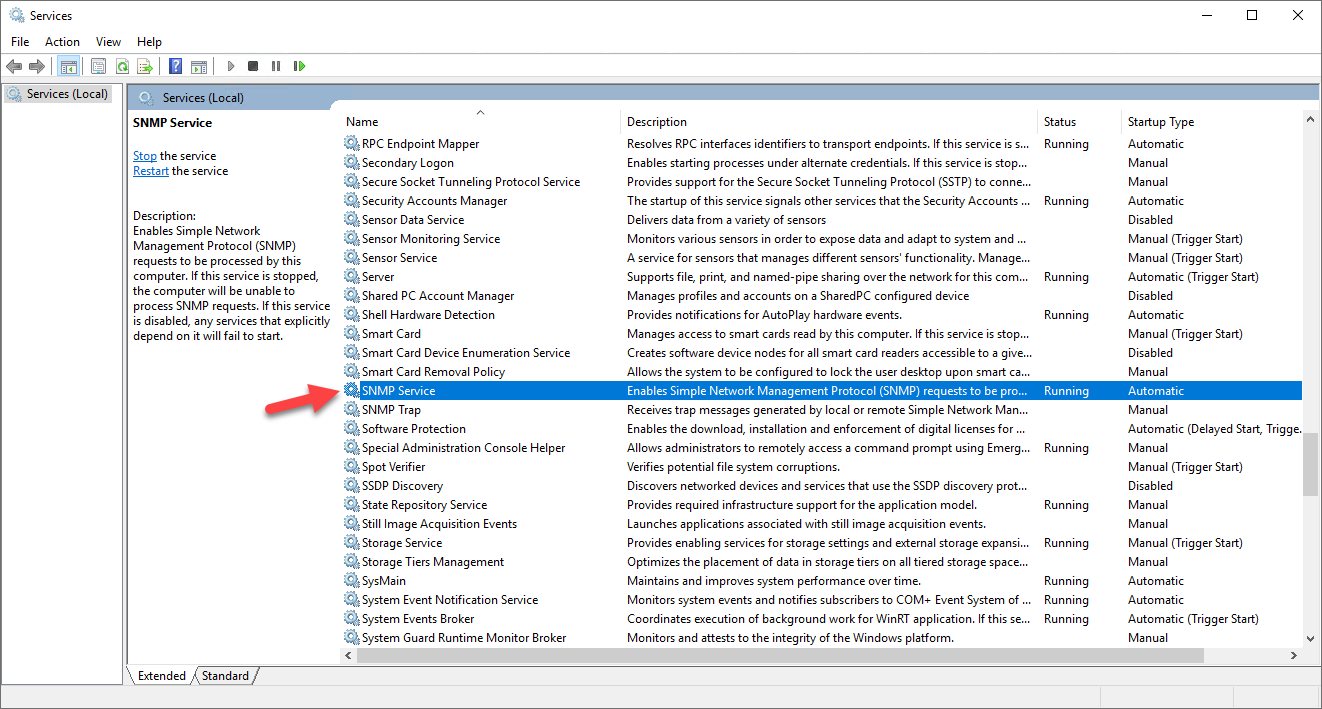
Type in Services in the Windows search field.
Open the Services app. Make a double click on the SNMP Service entry in the list.
Navigate to the Security register.
Adding an accepted community name (public) in the SNMP Service Properties is essential because it acts as a basic authentication mechanism for SNMP communication.
Without an accepted community name, SNMP monitoring tools like Zabbix, Nagios, or PRTG cannot authenticate or retrieve data from the server.
Click on the button.
At Community Name, enter public. public is a common default SNMP community name for READ ONLY access.
As a second step we need to limit the access to the SNMP interface to the Network Management System (NMS) host.
We do not recommend to accept from any host.
Click on again.
Activate Accept SNMP packets from these hosts.
Click on the button.
Add the host name or IP address of your monitoring system.
Click on again.
Click on . Click on .
Restart the SNMP Service.
Right-click on the SNMP Service.
Select Restart to stop and start the service again.
If the service is not running, select Start.
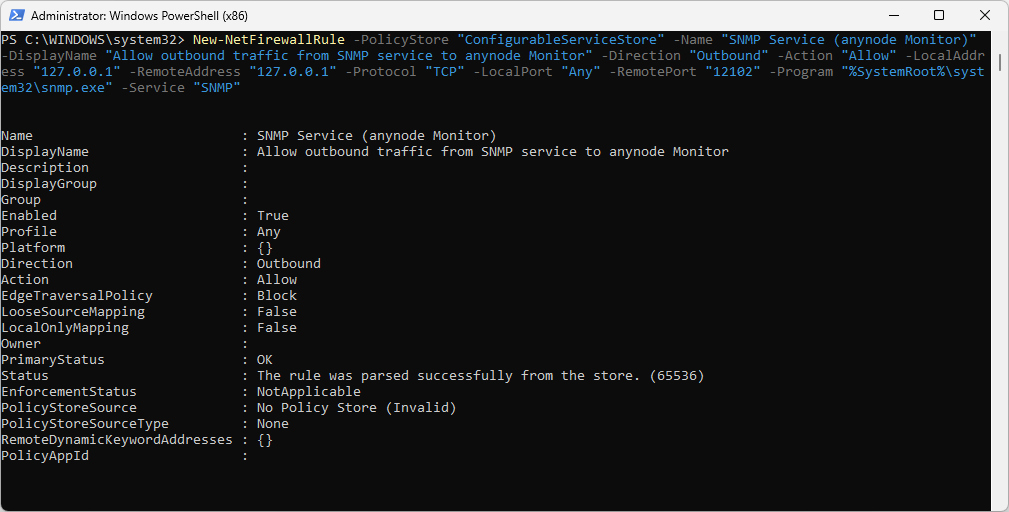
Internal Windows Firewall Configuration
Windows hardening may block SNMP monitoring.
Under certain Windows Server operating systems, there is a known issue that prevents the anynode SNMP service from communicating with the anynode Monitor. This is caused by Windows hardening policies, which block all network communication from the SNMP service except on port 161 (used for standard SNMP queries).
As a result, outbound connections (such as those required for SNMP-to-anynode Monitor communication on port 12102) are blocked by default.
How to check if a manual firewall rule is needed?
Run this command:
Test-NetConnection 127.0.0.1 -Port 12102
If the result shows TCPTestSucceeded = False, a firewall rule must be created to allow SNMP to communicate
with the anynode Monitor service.
Windows PowerShell Command
This issue cannot be resolved using the GUI-based Windows firewall configuration. To allow communication, a manual rule must be created using PowerShell.
Copy the following command as a single line into PowerShell: (Do not insert line breaks.)
Run the following command as Administrator in Windows PowerShell:
What This Rule Does:
-
Allows local outbound TCP traffic from the SNMP service (
snmp.exe) -
Targets port
12102, used by the anynode Monitor -
Applies only to localhost (
127.0.0.1) traffic -
Bypasses the hardening restriction for this specific case
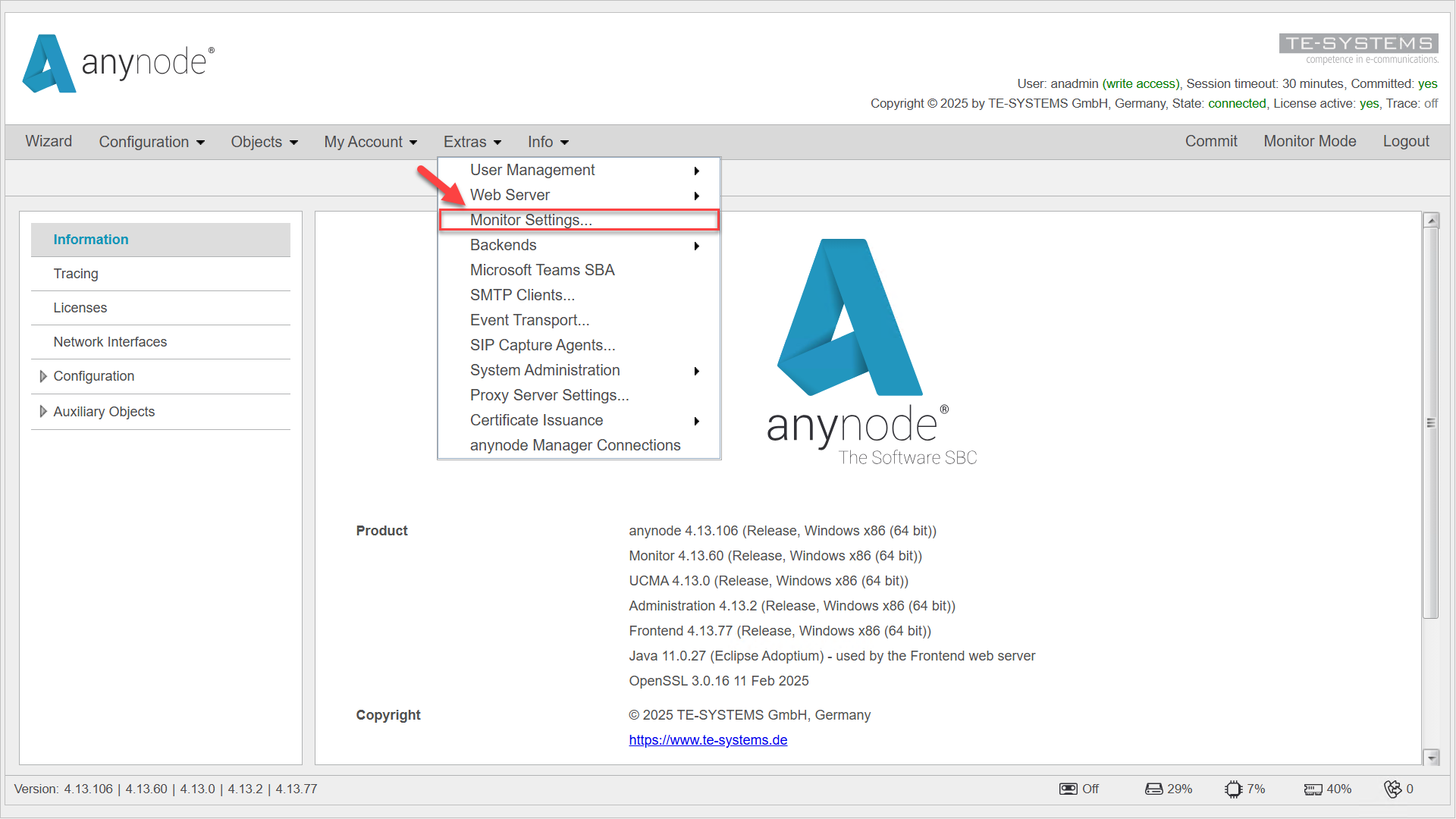
Configuration anynode Frontend (Windows)
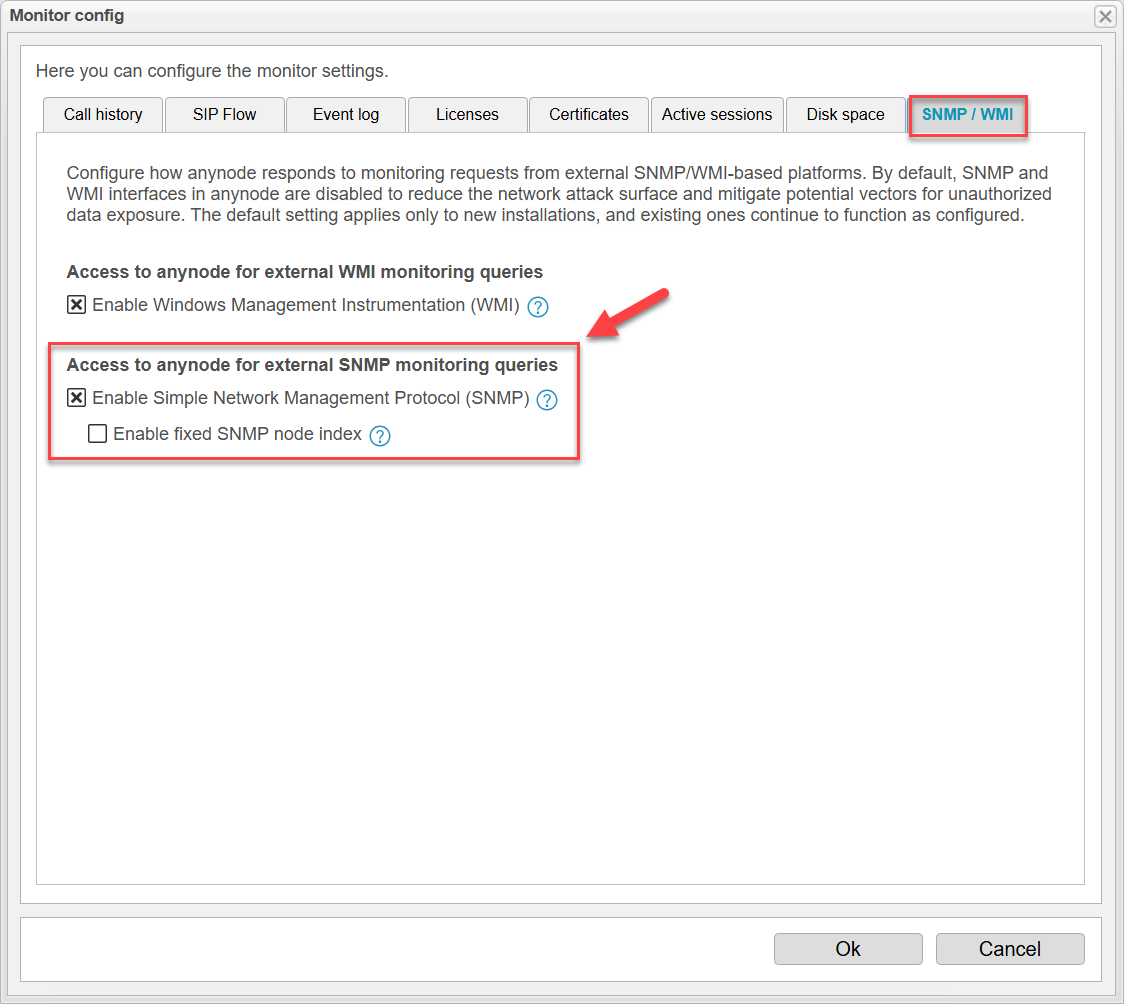
This section explains how to configure anynode to respond to monitoring requests from external SNMP or WMI-based platforms. By default, both SNMP and WMI interfaces are disabled in anynode to minimize the network attack surface and prevent potential unauthorized access to system information.
The default setting applies only to new installations, and existing ones continue to function as configured.
To modify the default settings for SNMP and WMI in anynode, open the anynode frontend and navigate to Extras -> Monitor Settings.
Then, select the SNMP / WMI tab to configure how anynode interfaces with external monitoring systems.
Navigate to Access to anynode for External SNMP Monitoring Queries.
Enable Simple Network Management Protocol (SNMP).
Click on .
Fixed SNMP Index
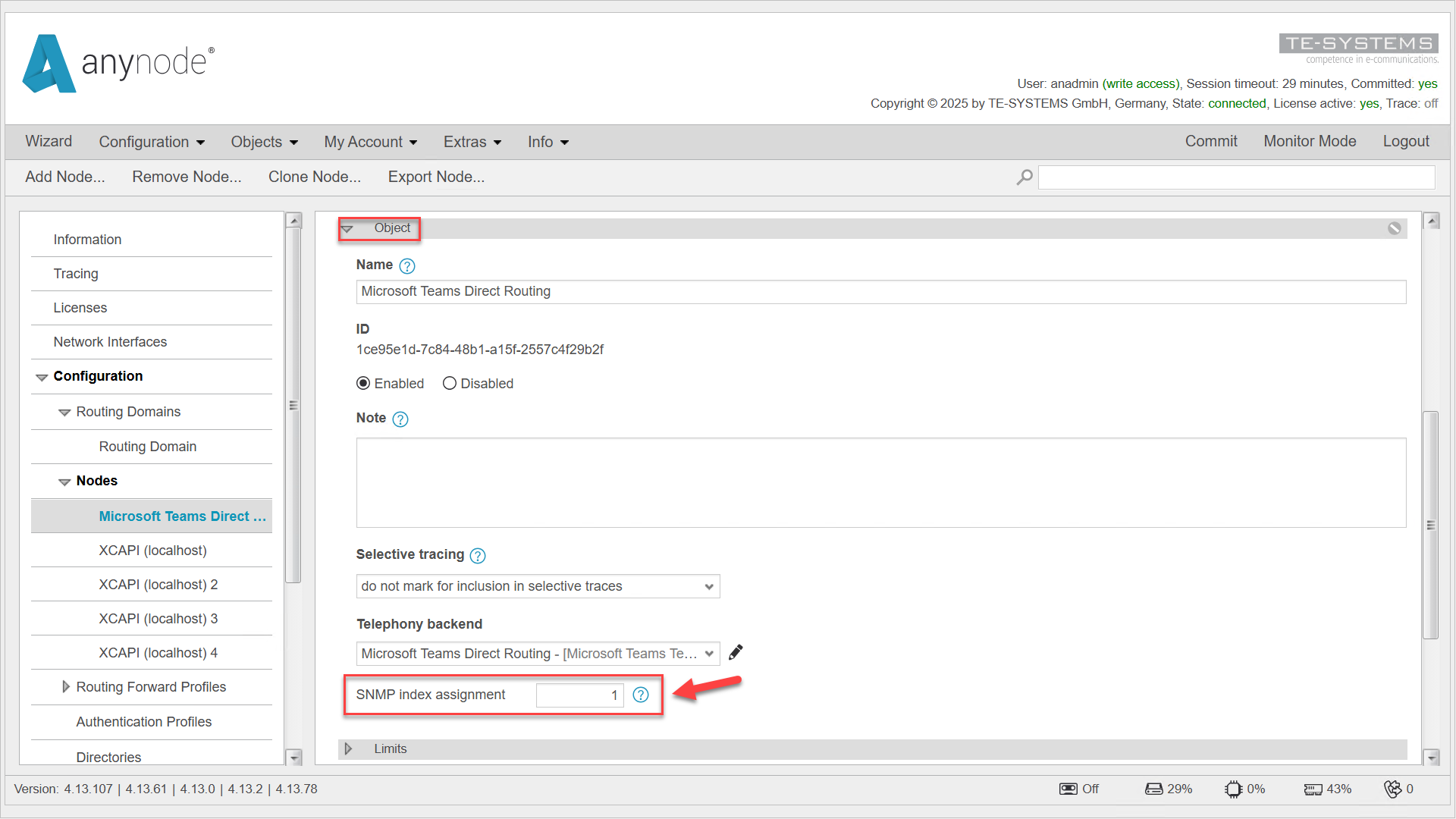
Enable fixed SNMP index in anynode whenever you plan to monitor indexed SNMP tables, especially for long-term graphing, alerting, or correlation of dynamic objects. The fixed index can be explicitly assigned within the node object configuration in anynode.
Navigate to the desired node object and open the Object register.
In SNMP monitoring, each node object in anynode is represented by an index within the SNMP table. By default, these indices are generated dynamically based on the current list of enabled nodes. As a result, indices can shift when nodes are temporarily disabled or re-enabled—potentially leading to inconsistencies or mismatches in external monitoring systems.
To avoid such issues, anynode allows administrators to manually assign a fixed SNMP index to each node.
Assign a unique and fixed index to each node to avoid conflicts or ambiguity across the SNMP table. If Fixed SNMP Index is not enabled in the Monitor Settings, any manually assigned index values will be ignored. In this case, indices continue to be generated dynamically based on the list of currently active nodes.
Click to apply and finalize the index assignment.
Troubleshooting Windows
In this chapter, we're diving into SNMP Troubleshooting for Windows. We know technical issues can be a bit of a headache, but don't worry – we've got some simple steps to help you pinpoint and fix the problem. So, let's roll up our sleeves and get started on solving that SNMP mystery together!
Ping the Host
First things first, let's make sure the monitoring server can reach the anynode host. This is a basic but crucial step. Here's how you can do it:
Ping from NMS to the anynode host: Use the IP address or hostname of the anynode host to perform the ping. This will help you verify if the network management system (NMS) can communicate with the anynode host.
ping<IP_or_hostname_of_anynode_host>
Check the response
If you receive replies, it means the NMS can reach the anynode host. If not, there might be a network issue that needs to be addressed.
By ensuring the monitoring server can reach the anynode host, you're taking the first step towards identifying and resolving any SNMP-related issues. Let's keep going and tackle the next steps together!
Check Windows Version
Windows 10 Home and Windows 11 Home editions do not include built-in support for SNMP (Simple Network Management Protocol). This feature is available only in the Pro, Enterprise, and Education editions of Windows.
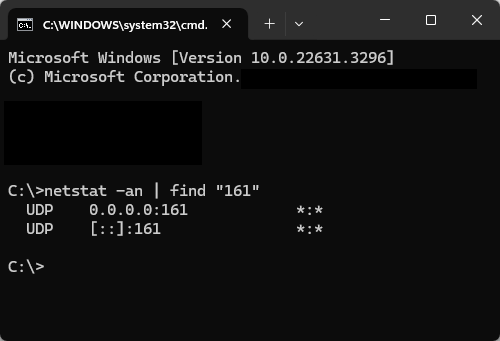
Using netstat to Verify SNMP Listening Ports
The netstat command is an essential troubleshooting tool to verify if SNMP is listening on the correct port
on Windows. Here's how you can use it:
Open Command Prompt as Administrator:
Press Win + R, type cmd, and press Ctrl + Shift + Enter to run as administrator.
Check SNMP Listening Port (161):
netstat -an | find "161"
This filters all active connections and listeners for the default SNMP port 161.
Look for a line similar to this:
Result Description
UDP 0.0.0.0:161 *:*
Protocol: UDP
Listening Address: 0.0.0.0 means SNMP is listening on all IPv4 addresses on the
machine, including any assigned IPs. If you see a specific IP instead of 0.0.0.0, SNMP is bound to that IP address only.
Port: 161 is the default SNMP port for receiving requests.
*:*: Indicates SNMP will accept connections from any remote source on port 161.
[::]:161
[::] This is the IPv6 equivalent of 0.0.0.0 in IPv4. It means the SNMP service is listening
on all IPv6 addresses of the machine, including:
-
Global IPv6 addresses
-
Link-local IPv6 addresses
-
Loopback (
[::1])
161 The port number SNMP uses for receiving requests.
*:* Indicates that the SNMP service will accept connections from any remote address on port 161.
UDP [::1]:161 *:*
Protocol: UDP
Listening Address: [::1] is the IPv6 loopback address
(IPv6 equivalent of 127.0.0.1).
Port: 161 (default for SNMP). This allows SNMP requests from the local machine
using IPv6.
If SNMP Is Not Listening
If no output is returned for ports 161 or 162:
Verify the SNMP Service:
Ensure the SNMP Service is running via: services.msc
Restart the service if needed net stop snmpnet start snmp
Check the firewall setting
Confirm that the firewall allows inbound UDP traffic for ports 161 and 162.
SNMP Configuration
Check the SNMP service configuration for proper settings (e.g., agent address, community strings, allowed hosts).
Check the SNMP service in Windows using the GUI
To check the SNMP service in Windows using the GUI, follow these steps:
Type in Services in the Windows search field. Open the Services app. In the Services window:
Scroll down the list to find SNMP Service.
If you're using traps, also look for SNMP Trap.
Look at the Status column:
If the service is running, it will say Running.
If it’s not running, the status will be blank.
To start or restart the SNMP service: Right-click on SNMP Service.
Select Start or Restart.
Check the Service Properties:
To view or configure SNMP settings:
Right-click on SNMP Service and select Properties.
Go to the Security tab:
Configure community strings and specify allowed hosts for SNMP access.
Refer to Windows Services list with SNMP Service. in the chapter Configuration Windows for more details.
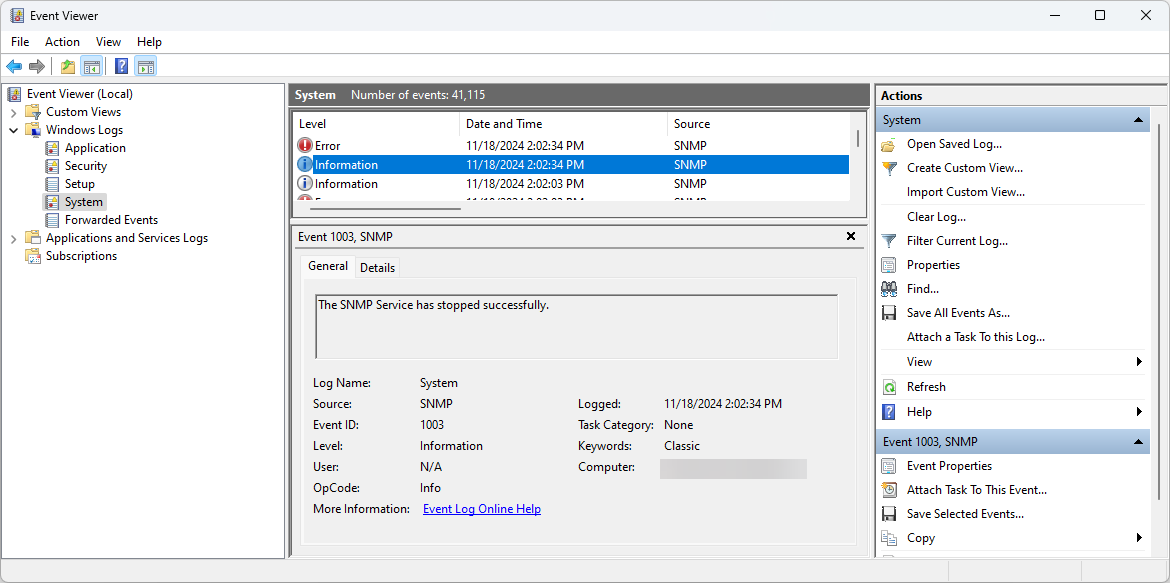
Check Windows Event Viewer
By checking the Event Viewer, you can identify problems with the SNMP service, configuration errors, or network issues affecting its operation.
Press Win + R to open the Run dialog.
Type eventvwr.msc and press Enter.
Navigate to Relevant Logs
The Event Viewer is organized into several categories of logs. For SNMP or general troubleshooting, check these areas:
Application Logs
Location:Event Viewer > Windows Logs > Application
What to look for: Errors or warnings related to applications, including SNMP-related issues.
System Logs
Location:Event Viewer > Windows Logs > System
What to look for: Errors or warnings related to system services, such as the SNMP service, drivers, or network-related problems.
Setup Logs (Optional)
Location:Event Viewer > Windows Logs > Setup
What to look for: Installation-related issues, if SNMP was recently installed.
Custom Views
If you have a monitoring tool or specific configuration, there may be a custom log created for SNMP or anynode-related activities.
Search for Specific Events
Use the Find feature:
Click Find in the right-hand pane.
Enter keywords such as SNMP, 161, or service.
Press Enter to locate specific events.
Analyze Event Details
Double-click an event to open its details. Focus on:
Event ID: Identifies the type of event. Look up the ID online for specific solutions.
Source: Indicates the service or application generating the event (e.g., SNMP).
Description: Provides a summary of what occurred.